Exchange API keys have become a critical yet overlooked risk vector in trading infrastructure security. These keys power automated strategies and connect directly to funds on centralized exchanges - but most trading firms treat them as an afterthought.
They’re rarely protected at the point of use, often exposed in runtime memory, and their compromise can lead to immediate, irreversible financial loss. No wonder they’ve become a favored target for attackers.
What’s worse: many teams operate under a false sense of security, relying on incomplete or outdated defenses.
In this paper you will learn about the risks behind Exchange API keys, how they are stolen and abused, and get a 30-day practical playbook to mitigate those risks.
Introduction
In the world of crypto trading, speed and automation rule. Machines, bots and backend services are continuously connected to centralized exchanges through API keys - the backbone of automated trading infrastructure.
These keys offer programmatic access to funds, permissions for trading, and, in many cases, withdrawal capabilities. In essence, they are private keys - but with fewer protections and far less scrutiny. Because exchanges treat API requests as bearer operations, any process that can sign with your key can move value in your account - instantly.
When compromised, exchange API keys don’t just expose positions - they compromise reputation and the entire business continuity as funds can be traded away, stolen, or manipulated within seconds.
Moreover, exchanges do not take any liability and security is the user’s responsibility solely. Security incidents happen often; however, many go unreported as they don’t leave on-chain traces.
Despite their importance, most trading teams fail to secure them with the same rigor they apply to private keys.
Let’s dive into the risks and where current defenses fail.
The Hidden Risks Behind Exchange API Keys
The nature of Exchange API keys makes them both powerful and vulnerable. They’re built for speed and automation - but not for security.
Unlike private keys, there’s no widely adopted best practice for their protection. This leaves a wide surface for abuse, both externally and internally.
Exchange API keys are:
- Always in use.
Trading machines and backend services frequently pull keys into memory, making them vulnerable to runtime attacks. - Easy to over-permission.
A key meant for trading only, can be simply misused for stealing funds. - Hard to monitor.
Once a key is active, there’s often no visibility into which process is using it, or how.
In many cases, these keys are copied into scripts, CI/CD pipelines, or secrets managers - leaving a trail of exposure points across cloud systems and dev environments.
Moreover, an observability stack is part of the attack surface: stack traces, APM breadcrumbs, crash dumps, and debug endpoints routinely capture secrets in cleartext.
Why Current Defenses Fail
Many trading firms assume they’re protected. But most of the standard solutions fall short - especially at runtime, which is when real attacks occur. Let’s break it down:
- IP Whitelisting sounds effective until you realize that most modern systems span cloud environments and dynamic IP ranges. If an attacker gets inside your environment or spoofs a trusted IP, this line of defense becomes irrelevant.
- “No Withdrawal” Permissions are often treated as a safety net. But attackers can still use the key to execute trades against you, create slippage, or manipulate pricing to their advantage - profiting while draining your positions.
- Secrets Managers protect keys at rest, but not in use. Once a key is loaded into a trading machine’s memory, it’s just another variable an attacker can capture - especially in systems with third-party dependencies or rogue insiders.
- Monitoring & Alerting may offer some insight, but they’re reactive by nature. By the time your system detects anomalous behavior, the key may have already been exploited.
- Hardware Security Modules (HSMs) provide high-assurance key storage, but they’re too slow for real-time trading. Worse, they can be vulnerable to blind signing, where attackers use legitimate requests to mask malicious behavior.
- Rotation ≠ Remediation. Rotating a key without fixing the runtime leak just resets the attacker’s timer. Most exchanges don’t enforce MFA on API calls; once a key is live, bearer semantics take over.
The pattern is clear: these solutions protect the key at rest, not in runtime - exactly when it matters most.
Threat Model: How Exchange API Keys Get Stolen (and Abused)
API keys are bearer credentials: if an attacker can sign with them, they can act as you. Common paths include:
- Phishing & developer‑workflow leaks: Keys copied for “quick tests,” pasted into terminals, tickets, screenshots, or shared docs; browser extensions or screen recorders collect them.
- Supply‑chain exposure: CI/CD logs, artifact caches, container images, and IaC repos quietly accumulate long‑lived keys.
- Runtime exfiltration: Memory scraping (/proc, ptrace, crash dumps), dynamic instrumentation (LD_PRELOAD), sidecars, APM/telemetry, or cloud debug agents capture secrets while the process runs.
- Insiders & over‑permissioning: SREs and quants reuse keys across services; a “trade‑only” key still enables toxic flow, slippage harvesting, or cross‑venue manipulation.
- Third‑party tools. Signal/bot platforms or “management” dashboards introduce another blast radius; their breaches become yours.
- Cloud misconfiguration: Overbroad roles let an attacker pivot from cloud metadata to your secrets store, then into trading machines.
Once inside, attackers can monetize in many ways, including slippage creation on illiquid pairs, cross‑account wash trades, fee‑rebate capture, leverage abuse, and latency arbitrage, often within minutes and without on‑chain traces.
The Runtime Blindspot
Most security tools focus on secure storage, making sure that only verified users and machines can access the key. However, none take care of security during usage, once the key is live in memory.
This creates a massive blind spot, and where attackers lurk, as any dev, machine, or service with access to the trading machine also has access to the full key.
Without runtime security, it’s impossible to tell if a key was misused - or by whom - until it’s too late.
Real‑World Incidents:What Exchange API‑Key Compromise Looks Like (When Reported)
These episodes show the same pattern: keys in memory are the payday; purely at‑rest controls aren’t enough.
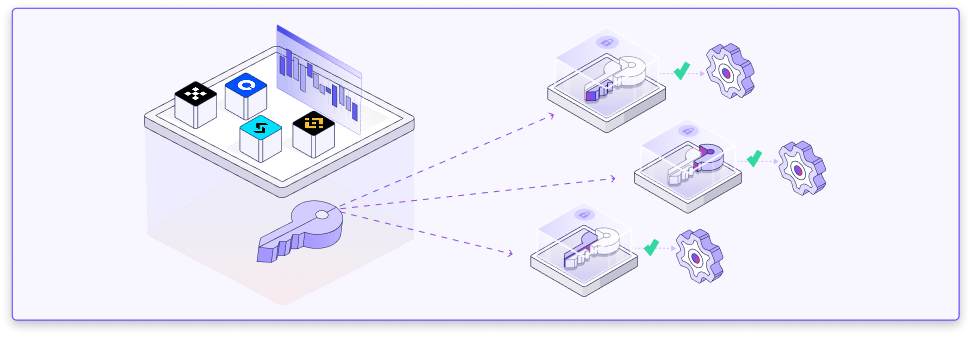
Rethinking the Model: Sodot’s Exchange API Vault
At Sodot, we believe exchange API keys deserve the same security standards as on-chain private keys.
That’s why we built the Exchange API Vault - the first key management solution designed specifically for automated trading, with high-frequency compatibility.
Main solution features:
- Runs inside Confidential Compute (TEE), ensuring keys are never exposed in memory.
- Uses Multi-Party Computation (MPC), so the full key never exists in one place.
- Enforces programmable policies before every signing request - even for trading-only permissions.
- Includes a “kill switch” for immediate run-time prevention.
- Secures the keys from the moment they’re imported from the exchange UI - not just at rest.
- It is built for real-time trading, with latency measured in microseconds.
- Offers full auditability - every action is logged.
With this model, raw key access is eliminated. Runtime misuse becomes impossible. Policy violations are blocked by default - not just logged after the fact.
Runtime Policy Examples (Policy‑as‑Code)
Saying “we enforce policy” is not enough; show the checks. Examples of pre‑trade gates that stop real attacks:
- Workload identity: only requests from an attested service (TEE measurement + code identity) are eligible to sign.
- Instrument allowlist: symbols/pairs explicitly allowed by strategy.
- Order‑type guardrails: disable market orders or restrict to post‑only.
- Notional & leverage caps: per‑order and rolling‑window limits; no cross‑margin borrow without policy.
- Slippage bounds: block if expected fill deviates >X bps from reference.
- Rate & burst limits: per symbol, venue, and account.
- Time‑of‑day windows: strategies trade only during approved sessions.
- Counterparty & venue scope: disallow new venues without approval.
- Kill‑switch conditions: volatility spikes, circuit breakers, or failed attestation ⇒ auto‑revoke session.
Adoption Playbook: Zero‑Exposure in 30 Days
Protecting exchange API keys requires a structured, step-by-step approach that addresses risks across the entire life-cycle. To move from reactive defenses to proactive resilience, trading firms can follow a clear adoption path designed to minimize exposure, enforce security at runtime, and ensure that security remains a constant priority: both during implementation and in ongoing operations through regular cybersecurity reviews and independent audits.
Here’s a practical 30-day roadmap to achieve zero exposure:
While implementing this roadmap, engaging trusted third parties for validation is highly recommended. Why? Independent assessments provide an external perspective, help identify blind spots, and ensure that defenses are effective under real-world attack scenarios.
Specialized security partners such as Halborn can add significant value in this process. By working with a security partner from system design through runtime implementation, trading firms can strengthen their infrastructure, reduce the blast radius of compromise, and maintain robust defenses against evolving threats.
Ultimately, resilience comes from making security a central pillar at every stage: from planning, to deployment, to ongoing operations.
Summary
Exchange API keys aren’t just back-office tools - they are powerful financial instruments. And yet, most trading firms still treat them like environment variables.
This is a mistake.
These keys move funds, execute trades, and enable automation at scale. They must be secured like private keys - at runtime, not just at rest.
Sodot’s Exchange API Vault brings enterprise-grade security to one of the industry’s most overlooked attack surfaces.
No blind spots. No key exposure. No compromises.
About Halborn
Halborn is a leading cybersecurity firm specializing in blockchain and digital asset security for financial institutions, Web3 companies, and infrastructure providers. Founded in 2019, Halborn delivers end-to-end solutions including smart contract auditing, advanced penetration testing, DLT advisory, and secure architecture consulting. Trusted by 600+ clients—including 10+ of largest banks and financial services institutions in the world—Halborn combines deep technical expertise with a technology-enabled service delivery model to secure the next generation of financial systems.